Recent Updates To MacOS Big Sur And CrowdStrike Falcon
Maybe your like
- Cyberattackers Are Invading Food Delivery
- Attackers Exploit Claude AI in Espionage Campaign
- New Security Features: DUO Verified Push and On-Campus Authentication Requests
- New Threats with ChatGPT Atlas Browser
- Silent Threats: The PassiveNeuron Cyber-Espionage Campaign
- Defenders and Deceivers: How AI Is Changing Cybersecurity Forever
- The Hidden Threat Behind Your Phone Number: Understanding Port-Out Attacks
- Using AI Responsibly

 You are at:Home»General Information»Recent Updates to macOS Big Sur and CrowdStrike Falcon General Information Recent Updates to macOS Big Sur and CrowdStrike FalconBy Louis PapaJanuary 12, 20211 Min Read
You are at:Home»General Information»Recent Updates to macOS Big Sur and CrowdStrike Falcon General Information Recent Updates to macOS Big Sur and CrowdStrike FalconBy Louis PapaJanuary 12, 20211 Min Read  Share Facebook Twitter LinkedIn Pinterest Copy Link
Share Facebook Twitter LinkedIn Pinterest Copy Link Following recent updates to both CrowdStrike Falcon and macOS, you may see the following message if after updating or restarting your Mac computer: “Falcon” Would Like to Filter Network Content.
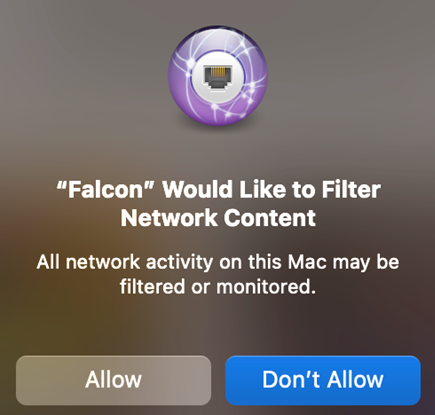
This message is legitimate. If you receive this message, here is what you need to do:
- Click “Allow.”
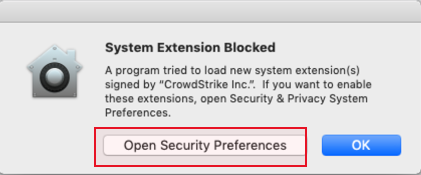
If a System Extension Blocked message appears (like in the image below):
- Click Open Security Preferences.
- Under the General tab click “Allow.” You may need to click the lock icon first to make changes.
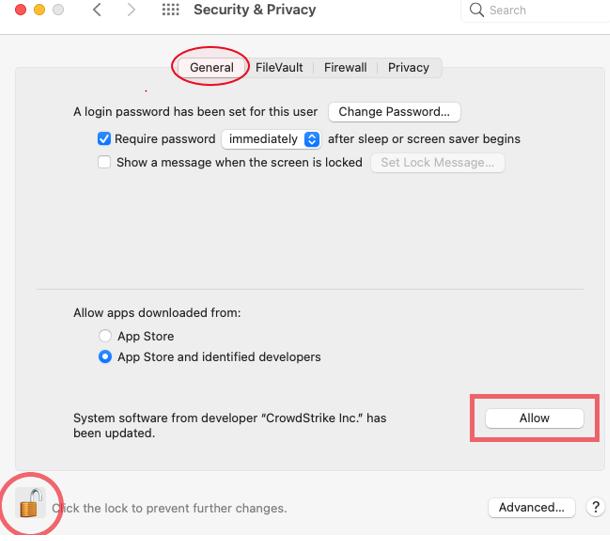
This only needs to be done once per machine and will not occur again with future updates.
If you already received this message and clicked “Don’t Allow,” simply restart your machine and you will be prompted again.
If you find the prompts are persisting even after following these instructions, or if you have questions, please contact IT Customer Care at 718-817-3999, or message [email protected].
Share this:
- X
Like this:
Loading... crowdstrike mac updates Previous ArticleFBI: Distance Learning Presents Opportunities for Cyber Criminals Next Article Scammers Targeting Students with Fake Grant OfferRelated Posts
New Security Features: DUO Verified Push and On-Campus Authentication Requests
Convenience or Compromise? The Rise of Quishing
What is CASB by Proofpoint?
Follow Us on Twitter!
Follow @FordhamSecureITMy Tweets Search for:Archives
Archives Select Month January 2026 (1) November 2025 (3) October 2025 (23) September 2025 (1) August 2025 (2) March 2025 (4) February 2025 (1) January 2025 (4) December 2024 (1) October 2024 (9) June 2024 (1) May 2024 (1) March 2024 (1) February 2024 (2) January 2024 (1) November 2023 (2) October 2023 (18) September 2023 (1) August 2023 (2) February 2023 (1) December 2022 (2) October 2022 (22) September 2022 (1) August 2022 (1) March 2022 (2) February 2022 (1) January 2022 (2) December 2021 (1) November 2021 (2) October 2021 (19) September 2021 (2) August 2021 (2) June 2021 (2) April 2021 (1) February 2021 (2) January 2021 (1) December 2020 (2) November 2020 (3) October 2020 (9) September 2020 (4) July 2020 (3) April 2020 (3) March 2020 (7) January 2020 (4) December 2019 (2) November 2019 (2) October 2019 (3) September 2019 (1) August 2019 (3) July 2019 (2) June 2019 (2) May 2019 (2) April 2019 (1) March 2019 (4) February 2019 (6) January 2019 (4) December 2018 (5) November 2018 (1) October 2018 (7) September 2018 (4) August 2018 (5) July 2018 (3) June 2018 (3) May 2018 (6) April 2018 (3) March 2018 (4) February 2018 (7) January 2018 (2) December 2017 (4) November 2017 (3) October 2017 (23) September 2017 (7) August 2017 (5) July 2017 (2) June 2017 (3) May 2017 (4) April 2017 (3) March 2017 (6) February 2017 (3) January 2017 (7) December 2016 (5) November 2016 (4) October 2016 (25) September 2016 (6) August 2016 (8) July 2016 (1) June 2016 (7) May 2016 (5) April 2016 (6) March 2016 (1) February 2016 (7) January 2016 (6) December 2015 (2) November 2015 (3) October 2015 (29) September 2015 (6) August 2015 (6) July 2015 (5) June 2015 (8) May 2015 (1) April 2015 (2) March 2015 (1) February 2015 (1) January 2015 (3) December 2014 (4) November 2014 (4) October 2014 (1) September 2014 (1) August 2014 (2) July 2014 (3) June 2014 (5) May 2014 (11) April 2014 (8) March 2014 (1) February 2014 (5) January 2014 (3) December 2013 (4) November 2013 (3) October 2013 (1) September 2013 (3) August 2013 (4) July 2013 (2) June 2013 (6) May 2013 (2) April 2013 (4) March 2013 (2) February 2013 (2) January 2013 (3) November 2012 (6) October 2012 (5) September 2012 (5) August 2012 (9) July 2012 (11) June 2012 (11) May 2012 (8) April 2012 (5) March 2012 (8) February 2012 (1) January 2012 (5) December 2011 (2) November 2011 (4) October 2011 (10) September 2011 (5) August 2011 (8) July 2011 (6) June 2011 (2) May 2011 (8) April 2011 (4) March 2011 (3) February 2011 (1) January 2011 (6) December 2010 (3) November 2010 (9) October 2010 (6) September 2010 (6) August 2010 (13) July 2010 (3) June 2010 (9) May 2010 (6) April 2010 (10) March 2010 (11) February 2010 (6) January 2010 (22) December 2009 (5) November 2009 (4) August 2009 (11) July 2009 (5) June 2009 (6) May 2009 (5) April 2009 (6) March 2009 (6) February 2009 (8) January 2009 (7) December 2008 (6) November 2008 (3) October 2008 (15) September 2008 (5) August 2008 (3)Categories
- AI (2)
- Alerts (385)
- CISO (21)
- Cyber Security Awareness Month Tip (171)
- Data Privacy Week (3)
- Executive Director (1)
- Exploits and Vulnerabilities (38)
- General Information (37)
- Identity and Access Management (13)
- Identity Theft (27)
- Jason Benedict (21)
- Legitimate Email (14)
- Malicious Email (26)
- Mobile (27)
- Network Security (3)
- News and Events (146)
- Newsletter (13)
- Password (19)
- Phishing (337)
- Phishing Email (340)
- Privacy (11)
- Ransomware (11)
- Scam (109)
- Security Awareness (281)
- Security Guides (36)
- Social Engineering (13)
- SPAM (40)
- Suspicious (7)
- Telework (2)
- Teleworking (3)
- Trojan (7)
- Uncategorized (9)
- Virtual Meeting (4)
- Virus (31)
- Viruses (8)
- World Backup Day (1)
- Zoom (6)
Tag Cloud
Alerts Artificial Intelligence Backups breach cell phones CISO Cyber Security Awareness Month Cybersecurity Awareness Month Tip Cybersecurity Month Data Privacy Device email Exploits and Vulnerabilities firewalls fraud General Information Identity and Access Management Identity Theft Information Security Guides Jason Benedict Legitimate Email malicious email Mobile Multi-Factor Authentication networks Network Security News and Events Newsletter online safety Password Phishing Phishing Email Privacy ransomware scam Security Awareness social engineering Social Media spam trojan Virus Viruses Wireless wire transfer scam zoom SubmitType above and press Enter to search. Press Esc to cancel.
%dTag » What Is Falcon On Mac
-
Falcon Endpoint Security For MacOS - CrowdStrike
-
Falcon For Mac OS | Data Sheet - CrowdStrike
-
CrowdStrike Falcon - University IT
-
CrowdStrike Falcon On The App Store
-
What Is Falcon On My Mac? - Book Revise
-
Mac App 'Falcon' V6.45 Download
-
Installing The CrowdStrike Falcon Sensor For MacOS - Duke OIT
-
What Is The Falcon App On Mac? - Handlebar
-
Install And Uninstall The Crowdstrike Falcon Sensor On MacOS
-
MacOS Falcon Sensor Deployment - Kevin Guay
-
CrowdStrike Falcon Pro For Mac Achieves 100% Malware Protection ...
-
How Do I Delete The Falcon Client Application In MacOS - Ask Different
-
CrowdStrike Falcon - Installation Instructions - IS&T Contributions
-
Endpoint Protection: CrowdStrike Removal - Boston University