Sms | Hackaday
Maybe your like

One of the most annoying things about keyboard and mouse input has got to be the need to constantly switch between the two. Ever wish there was a single solution that combined them with elegance? Then you should definitely check out [lemosbor]’s Lapa keyboard, where the right half includes a mouse sensor.

Let me just say that I love the look of this keyboard, and I don’t normally like black and brown together. But that oak — that oak is classy, and it looks good with the resin-and-varnish case. If you can handle a 36-key board — I myself cannot — then this would probably be a game changer. There are even slots for your palms to breathe.
Unfortunately it’s not open source, but a girl can dream, right? In the reddit post, [lemosbor] says that they would be interested in selling the next version, provided it’s the final one.
Continue reading “Keebin’ With Kristina: The One With The Keyboard-Mouse” →

Among us Hackaday writers, there are quite a few enthusiasts for retro artifacts – and it gets even better when they’re combined in an unusual way. So, when we get a tip about a build like this by [Sam Christy], our hands sure start itching.
The story of this texting typewriter is one that beautifully blends nostalgia and modern technology. [Sam], an engineering teacher, transformed a Panasonic T36 typewriter into a device that can receive SMS messages, print them out, and even display the sender’s name and timestamp. For enthusiasts of retro gadgets, this creation bridges the gap between analog charm and digital convenience.
What makes [Sam]’s hack particularly exciting is its adaptability. By effectively replacing the original keyboard with an ESP32 microcontroller, he designed the setup to work with almost any electric typewriter. The project involves I2C communication, multiplexer circuits, and SMS management via Twilio. The paper feed uses an “infinite” roll of typing paper—something [Sam] humorously notes as outlasting magnetic tape for storage longevity.
Beyond receiving messages, [Sam] is working on features like replying to texts directly from the typewriter. For those still familiar with the art form of typing on a typewriter: how would you elegantly combine these old machines with modern technology? While you’re thinking, don’t overlook part two, which gives a deeper insight in the software behind this marvel!
Continue reading “Back To The Future Of Texting: SMS On A Panasonic Typewriter” →
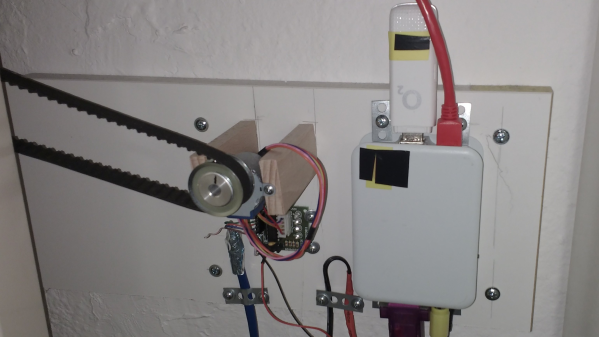
Hackaday.io user [mabe42] works during the week away from their home city and rents a small apartment locally to make this life practical. However, the heating system, a night-storage system, is not so practical. They needed a way to remotely control the unit so that the place was habitable after a long winter commute; lacking internet connectivity, they devised a sensible solution to create an SMS-controlled remote heating controller.
The controller runs atop an old Raspberry Pi B inside a 3D-printed case. Seeing such an old board given a real job to do is nice. Connectivity is via a USB UMTS stick which handles the SMS over the cellular network. The controller knob for the heater thermostat (not shown) is attached via a toothed belt to a pully and a 28BYJ-48 5V geared stepper motor. Temperature measurement is via the ubiquitous DS1820 module, which hooks straight up to the GPIO on the Pi and works out of the box with many one-wire drivers.
The software is built on top of Gammu, which handles the interface to the UMTS device. Daily and historical temperature ranges are sent via SMS so [mabe42] can decide how to configure the heating before their arrival. The rest of the software stack is in Python, as per this (German-language) GitHub project.
While we were thinking about storage heating systems (and how much of a pain they are), we came across this demonstration of how to build one yourself.


If you’re looking for a good excuse to finally buy a drone, you probably can’t do better than claiming it can save your life.
Granted, you may never find yourself in the position of being stuck in a raging snowstorm in the middle of the Oregon wilderness, but if you do, this is a good one to keep in mind. According to news stories and the Lane County Sheriff Search and Rescue Facebook page, an unnamed motorist who was trying to negotiate an unmaintained road through the remote Willamette National Forest got stuck in the snow. This put him in a bad situation, because not only was he out of cell range, but nobody knew where he was or even that he was traveling, so he wouldn’t be missed for days.
Thankfully, the unlucky motorist played all his cards right. Rather than wandering off on foot in search of help, he stayed with his vehicle, which provided shelter from the elements. Conveniently, he also happened to have a drone along with him, which provided him with an opportunity to get some help. After typing a detailed text message to a friend describing his situation and exact location, he attached the phone to his drone and sent it straight up a couple of hundred feet — enough to get a line-of-sight connection to a cell tower. Note that the image above is a reenactment by the Search and Rescue team; it’s not clear how the resourceful motorist rigged up the drone, but we’re going to guess duct tape was involved.
When he brought the drone back down a few minutes later, he found that the queued text had been sent, and the cavalry was on the way. The Search and Rescue unit was able to locate him, and as a bonus, also found someone else nearby who had been stranded for days. So it was a win all around thanks to some clever thinking and a little technology.
For all the convenience and indispensability of having access to the sum total of human knowledge in the palm of your hand, the actual process of acquiring and configuring a smartphone can be an incredibly frustrating experience. Standing in those endless queues at the cell phone store, jumping through the administrative hoops, and staring in sticker shock at a device that’s likely to end its life dunked in a toilet all contribute to the frustration.
But for my money, the real trouble starts once you get past all that stuff and start trying to set up the new phone just right. Sure, most phone manufacturers make it fairly easy to clone your old phone onto the new one, but there are always hiccups. And for something that gets as tightly integrated into the workflows of your daily life as cell phones do, that can be a real bummer. Especially when you find out that your shiny new phone can’t do something you absolutely depend on.
Continue reading “The New-Phone Blues: A Reminder That Hackers Shouldn’t Settle” →

The modern smartphone is a marvel of sensors, radios, inputs, outputs, and processing power. In particular, some of those radios, such as WiFi and cellular, have grown fiendishly complex over the years. Even when that complexity is compressed down for the user into the one-dimensional space of the signal strength bars at the top of your phone. So when [David Burgess] was asked to look at some cellphone records of text messages and figure out where some of the more mysterious messages were coming from, it led him down a rabbit hole into the dark arts behind the glowing phone screen.
The number in question was 1111340002, sent by a phone connected to AT&T at the time, and was crucial for a legal case around distracted driving. [David’s] tools in his investigation were YateBTS (a cellular network simulator), SimTrace2 (pictured above), and old reliable Wireshark. Since the number isn’t a specific phone number and is not reachable from the public phone network, it must be a unique number inside AT&T processed by one particular AT&T SMSC (Short Message service center). The SMSC in question is in Atlanta and isn’t a typical texting center, so it must have some particular purpose. The message’s payload is raw binary rather than text, and [David] has done a pretty good job of decoding the majority of the format.
The most exciting revelation in this journey is that the phone (in the traditional sense) does not send this message. The processor on the phone does not know this message and executes no code to send it. Instead, the SIM card itself sends it. The SIM card is connected directly to the baseband processor on the phone, and the baseband polls the sim every so often, asking for any commands. One of those commands is an SMS (though many other commands have worrying consequences).
The SMS that [David] was chasing is triggered whenever a SIM detects a new IMEI, and the message lets the network know what about the previous and current IMEI. However, in the case of this message, it was unlikely that the SIM changed phones, so what happened? After some additional lab work and the deposition of an AT&T employee, [David] showed that a baseband firmware update would also trigger this SMS.
It’s a fascinating journey into the fragmented world of a smartphone’s minds and [David] does a fantastic job on the writeup. If you’re interested in sniffing wireless accessories, you will enjoy this soundbar’s wireless protocol laid bare.

There seems to be a new trend in malware, targeting developers and their development and build processes. The appeal is obvious: rather than working to build and market a malicious application, an attacker just needs to infect a development machine. The hapless infected developers can now do the hard work to spread the malicious payload.
The newest example is XcodeSpy, discovered by a researcher who chose to remain anonymous. It works by using the Xcode IDE’s Run Script function to, well, run a script that completely backdoors your computer. The instance was found in a repackaged open source project, TabBarInteraction, but they’re just innocent victims. It was simple enough for someone to insert a script in the build process, and distribute the new, doped package. It’s probably not the only one out there, so watch out for Run Scripts with obfuscated payloads.
Continue reading “This Week In Security: XcodeSpy, Insecure SMS, And Partial Redactions” →
Posts navigation ← Older posts Search Search for: Never miss a hack Follow on facebook Follow on twitter Follow on youtube Follow on rss Contact us Subscribe If you missed it-

Pokemon Go Had Players Capturing More Than They Realized
14 Comments -

German Fireball’s 15 Minutes Of Fame
10 Comments -

The “Tin Blimp” Was A Neither Tin Nor A Blimp: The Detroit ZMC-2 Story
22 Comments -

Secure Communication, Buried In A News App
25 Comments -

New Artemis Plan Returns To Apollo Playbook
54 Comments
-

Blood Tests Could Provide Early Warning Of Alzheimers Disease
2 Comments -

Ask Hackaday: What Will An LLM Be Good For In The Plateau Of Productivity?
69 Comments -

Hackaday Links: March 8, 2026
8 Comments -

Choice, Control, And Interruption
47 Comments -

Hackaday Podcast Episode 360: Cool Rubber Bands, Science-y Stuff, And The Whys Of Office Supplies
7 Comments
-

Pokemon Go Had Players Capturing More Than They Realized
14 Comments -

German Fireball’s 15 Minutes Of Fame
10 Comments -

The “Tin Blimp” Was A Neither Tin Nor A Blimp: The Detroit ZMC-2 Story
22 Comments -

Secure Communication, Buried In A News App
25 Comments -

New Artemis Plan Returns To Apollo Playbook
54 Comments
-

Blood Tests Could Provide Early Warning Of Alzheimers Disease
2 Comments -

Ask Hackaday: What Will An LLM Be Good For In The Plateau Of Productivity?
69 Comments -

Hackaday Links: March 8, 2026
8 Comments -

Choice, Control, And Interruption
47 Comments -

Hackaday Podcast Episode 360: Cool Rubber Bands, Science-y Stuff, And The Whys Of Office Supplies
7 Comments
- charliex on Pokemon Go Had Players Capturing More Than They Realized
- Christoph on A Radio Power Amplifier For Not A Lot
- JustSayin on How Would A Field Sequential Home Computer Have Worked?
- Greg A on Selective Ironing Adds Designs To 3D Prints
- smellsofbikes on Pokemon Go Had Players Capturing More Than They Realized
- ialonepossessthetruth on How Would A Field Sequential Home Computer Have Worked?
- Bill on How Would A Field Sequential Home Computer Have Worked?
- Steven Clark on Correcting Color Blindness With DLP Projectors
- dan on Open Source Radar Has Up To 20 KM Range
- jpa on Hands On With Creality’s New M1 Filament Maker
Tag » How To Hack Mobile Sms
-
Syniverse Short Message Service (SMS) Hack And Two Factor ...
-
How Hackers Can Use Message Mirroring Apps To See All Your SMS ...
-
Hacking SMS MFA Systems|WatchGuard Blog
-
SMS Tips, Tricks And Hacks - MessageMedia
-
Hack-sms · GitHub Topics
-
How To Hack A Phone: 7 Common Attack Methods Explained
-
Top 10 SMS Marketing Hacks Of All Time - MobileMonkey
-
Your Phone Number Is All A Hacker Needs To Read Texts, Listen To Calls ...
-
How To Hack Someone's Text Messages? - Alucare
-
Android Phones Can Be Hacked With A Simple Text - CNN Business
-
Can One Hack A Phone Through Sending SMS? How Is It Possible ...
-
This SMS Hack Could Steal Your Text Messages - YouTube
-
Dangerous Texts: Preventing SMS Cracking - Infosec Resources