What Is A SID (Security Identifier)? - TechTarget
Maybe your like
- Home
- Application and platform security
 By
By - Peter Loshin, Former Senior Technology Editor
What is a security identifier (SID)?
In the context of Windows computing and Microsoft Active Directory (AD), a security identifier (SID) is a unique value that is used to identify any security entity that the Windows operating system (OS) can authenticate. A security entity can be a security principal -- a user account, a computer account or a process started by those accounts -- or it can be a security group.
All Windows objects that can be uniquely identified by name store their SID, along with any discretionary access control lists and system ACLs, in a security descriptor data structure.
How do SIDs work?
Microsoft Windows security depends on SIDs for authentication. Windows server OSes use SIDs to uniquely identify accounts on the local computer in a persistent way: A user account name could change, but since the SID stays the same, that account can still be identified.
When a computer joins a domain, the domain controller grants it a Domain SID for authentication purposes in the domain. ACLs include lists of SIDs for security principals and groups that are authorized for access to that domain.
There are also well-known SIDs, which are identifiers for generic groups and users that are valid and persistent on all Windows systems. For example, two commonly used well-known SIDs specify the all users group or the Null SID, which is a group that has no members.
Why are SIDs used?
SIDs are used as a unique identifier for entities that use Windows. SIDs are a component of a security database that security authorities can use to identify the user and the permissions that user is entitled to.
When users log on to a Windows system, the system generates an access token that includes the user SID, the SID of any groups the user belongs to and the user privilege level. This access token can be authenticated against an ACL to determine what the user can access.
What is the format of SIDs?
A SID is a data structure that organizes SID information in a logical structure consisting of values, including the following:
- Revision is the version level of the SID and is required to be initialized as 0x01.
- SubAuthorityCount is the number of subauthorities in the SID.
- IdentifierAuthority is the entity that created the SID, usually represented as three 16-bit numbers separated by hyphens.
- SubAuthority is a component of the SID's domain, and an SID may include up to 15 subauthorities, each of which is identified by a 32-bit subauthority value.
The SID structure is stored as binary data and converted to a string format for reading. Basic syntax rules for SIDs include the following:
- All SIDs start with the letter "S."
- Individual components of the SID are separated by hyphens.
- Individual components of the SID are strings composed of numbers and hyphens.
- SIDs are composed of four components:
- revision level
- identifier authority
- domain identifier
- relative identifier
A typical SID looks like this:
S-1-5-21-1004336348-1177238915-682003330-512This SID is the unique identifier for Microsoft's example domain for the Domain Admins group at Contoso Ltd. Contoso is a fictional company often used as an example for Microsoft domains. This SID consists of four discrete components in addition to the "S-" prefix that identifies it as an SID. The other components are the following:
- 1 indicates the revision level.
- 5 is the identifier authority, indicating the NT authority; this value is only used for Microsoft Windows installations. Valid values are 0 through 5, indicating the following:
- 0 null authority
- 1 world authority
- 2 local authority
- 3 creator authority
- 4 nonunique authority
- 5 NT authority
- 21-1004336348-1177238915-682003330 is the domain identifier that uniquely identifies Contoso as the domain.
- 512 is the relative ID specifying the Domain Admins group within the Contoso domain.
How to find a SID number
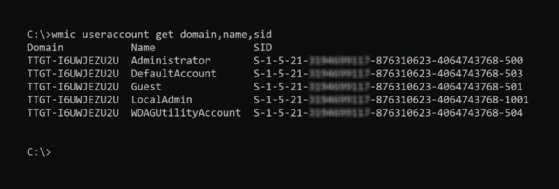
SIDs are stored in the Windows registry and can be found using Windows Registry Editor. To discover SIDs using the Windows command prompt, enter the following command:
wmic useraccount get domain,name,sidWMIC stands for Windows Management Instrumentation Command, a software utility that enables users to perform Windows administration tasks through the command line.
To get the SID for the current logged-in user from the command prompt, enter the following command:
whoami /user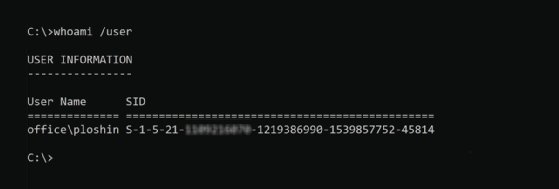
SID is just one component of many in the Microsoft AD security infrastructure. Take this quiz to test your AD knowledge, or read on to learn more about techniques for troubleshooting AD issues.
Continue Reading About security identifier (SID)
- Comparing macOS vs. Windows security
- Set up users with key PowerShell Active Directory commands
- How to locate privileged accounts in Active Directory
- Construct a solid Active Directory password policy
- Explore the benefits of Azure AD vs. on-prem AD
Related Terms
What is a message authentication code (MAC)? How it works and best practices A message authentication code (MAC) is a cryptographic checksum applied to a message to guarantee its integrity and authenticity. See complete definition What is file integrity monitoring (FIM)? File Integrity Monitoring (FIM) is a security process that continuously monitors and analyzes the integrity of an organization's ... See complete definition What is governance, risk and compliance (GRC)? Governance, risk and compliance (GRC) refers to an organization's strategy, or framework, for handling the interdependencies of ... See complete definitionDig Deeper on Application and platform security
-
![]()
Microsoft 365 Administration Expert Questions and Answers
 By: Cameron McKenzie
By: Cameron McKenzie -
![]()
Fix Windows 11 remote desktop credentials that don't work
 By: Marius Sandbu
By: Marius Sandbu -
![]()
Sysprep (System Preparation Tool)
 By: Brien Posey
By: Brien Posey -
![]()
How to perform an AD group membership backup and restore
 By: Mike Kanakos
By: Mike Kanakos
- 2023 Business Resilience Strategies –Dell Technologies
- Driving Digital Transformation in Financial Services –Dell Technologies
- See More
- The Mind Of The CISO: Closing The Gap Between Reaction And Readiness –Trellix
- A Process is No One –SpecterOps
- Networking
- CIO
- Enterprise Desktop
- Cloud Computing
- Computer Weekly
- 5 principles of change management in networking
Network change management includes five principles, including risk analysis and peer review. These best practices can help ...
- How network efficiency advances ESG goals
From SDN to green electricity, network optimization plays a critical role in helping enterprises reduce emissions, cut costs and ...
- How to build a private 5G network architecture
A private 5G network can provide organizations with a powerful new option for their wireless environments. Here are the major ...
- AI transformation is inevitable but requires change management
Enterprises are split on AI adoption speed. While some take an aggressive workforce overhaul, others preach more careful ...
- 12 top business process management tools for 2026
BPM platforms are becoming a business transformation engine as vendors infuse their tools with powerful AI and automation ...
- What Big Tech's AI spending means for your IT budget
Hyperscalers are spending billions on AI. CIOs can't match that scale -- but they can adopt smarter budgeting strategies to ...
- How Windows 11 Safe Mode works and when to use it
Windows 11 Safe Mode gives IT leaders a reliable way to diagnose failures, restore access to broken systems and strengthen ...
- How Windows 11 Print Management can fix printer issues
IT admins can use Print Management in Windows 11 to manage all printers connected to a device, troubleshoot problems and restart ...
- How to migrate applications to Windows 11
As Windows 10 support ends, organizations must plan Windows 11 migrations carefully. Assess apps, data and device configurations ...
- GenAI drives $119B cloud revenue in Q4
Q4 cloud infrastructure service revenues reach $119.1 billion, bringing the 2025 total to $419 billion. See how much market share...
- Cloud infrastructure suffers AI growing pains
Will $5 trillion in AI infrastructure investment be enough? Cloud providers facing that question must also yield a return, ...
- 8 reasons why IT leaders are embracing cloud repatriation
As IT leaders aggressively re-allocate capital to fund new AI initiatives, repatriation offers both savings and greater control, ...
- UK direct-to-device satellite connectivity takes off with Virgin Media O2
Leading UK mobile operator switches on pace comms service in a move to make UK the first country in Europe to go live with ...
- NTT Data, Ericsson team to scale private 5G, physical AI for enterprises
Global comms tech provider forges global partnership with business and technology services firm to establish 5G as the ...
- Connectivity, AI drive fleet safety, productivity and decision-making
Report into state of fleet technology across US reveals three key priorities for the year: increasing productivity, reducing ...
Tag » Active Directory Search User By Sid
-
How To Find User Or Group From SID - Windows Server
-
Get SID For All Users In AD - Microsoft Q&A
-
Retrieve User Details From Active Directory Using SID - Server Fault
-
How To Convert SID To User/Group Name And User To SID?
-
How To Search Active Directory By 'objectSid' Using PowerShell
-
Searching AD For A User Account With A SID - Jeff Schertz's Blog
-
Searching For Active Directory User Using SID Across Multiple Sub ...
-
How To Find A User's Security Identifier (SID) In Windows - Lifewire
-
PowerShell - Get User SID In Active Directory - ShellGeek
-
Get-AdUser: Finding Active Directory Users With PowerShell
-
Find SID In Active Directory Users And Computers Using PowerShell
-
Finding An Active Directory User's SID Using PowerShell
-
User And Group Commands In AD Bridge - BeyondTrust
-
ARCHIVED: In Windows, What Is The SID (security Identifier)? - IU KB



