What Is GUID? - TechTarget
Maybe your like
- Home
- IT operations and infrastructure management
 By
By - Alexander S. Gillis, Technical Writer and Editor
What is GUID?
A GUID (globally unique identifier) is a 128-bit text string that represents an identification (ID). Organizations generate GUIDs when a unique reference number is needed to identify information on a computer or network. A GUID can be used to ID hardware, software, accounts, documents and other items. The term is also often used in software created by Microsoft.
GUIDs are useful when a unique identifier is needed that has a very low probability of being repeated. The text string can be used across all computers and networks. GUIDs are like serial numbers, as organizations use them to ensure database records are not duplicated and all data has an ID that is unique across different databases.
GUID was a term first used by Microsoft to refer to a specific variant of a similar term, Universally Unique Identifier, or UUID. Since then, the terms have been combined, with the RFC 4122 specification using them synonymously. Different versions of GUIDs follow the RFC 4122 specification.
How does GUID work?
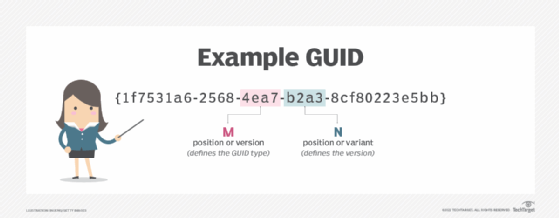
GUIDs are constructed in a sequence of digits that equal 128 bits. The ID is in hexadecimal digits, meaning it uses the numbers 0 through 9 and letters A through F. The hexadecimal digits are grouped in a format that is 36 characters long -- 32 hexadecimal characters grouped as 8-4-4-4-12 and separated by four hyphens: {XXXXXXXX-XXXX-XXXX-XXXX-XXXXXXXXXXXX}.
Users do not need to rely on a centralized authority to administer GUIDs, as anyone can use a generation algorithm to create a GUID. Individuals and organizations can create GUIDs using a free GUID generator that is available online. An online generator constructs a unique GUID according to RFC 4122. When creating a GUID, users should note the timestamp, clock sequence and the node ID -- such as a Media Access Control (MAC) address.
What is GUID used for?
GUIDs are designed to be used nearly everywhere a unique identifier is needed. They can be used to uniquely identify COM entities on Windows, for example, and are also used to identify the following:
- user accounts;
- component identifiers that identify parts and components that are part of a final product, such as a car;
- database keys to merge database records;
- documents, such as Word documents and desktop files;
- hardware, such as servers or monitors;
- interfaces, such as operating systems; and
- software applications.
Types and variants of GUIDs
There are five different versions of GUIDs, most of which follow the RFC 4122 specification.
- Date-time and MAC address. This version generates IDs with the current time and client MAC
- Distributed Computing Environment Security. This version is constructed similarly to the Date-time and MAC address GUID format but replaces the first 4 bytes of the timestamp with the user's Portable Operating System Interface UID. It was defined in the early 1990s and is rarely used. This version is also not defined in RFC4122.
- Message-digest algorithm (MD5) hash and namespace. This version generates IDs using MD5 hash and a namespace converted into hexadecimal. GUIDs generated from the same namespace are identical in this format.
- Randomly generated digits. Except for 6 bits that refer to version and variant bits, this version is generated using random bits. There is no specification on how the random digits should be generated, meaning that pseudo-random generators can be used.
- Secure Hash Algorithm 1 (SHA-1) hash and namespace. This version is constructed similarly to MD5 hash and namespace, but uses SHA-1 for hashing instead of MD5.
Benefits of GUID
Some potential benefits that come with GUIDs include:
- No central authority is needed, which means GUIDs can be generated internally for different uses.
- The 128-bit size is large enough that it is extremely unlikely to get a repeating ID.
- Merging databases with GUIDs is possible because it is extremely unlikely that two items share the same ID.
- GUIDs can be generated rapidly and offline.
Learn how GUIDs are used in designing a custom Hyper-V Integration Service component in this article.
Continue Reading About GUID (global unique identifier)
- Cryptography basics: Symmetric key encryption algorithms
- Get back on the mend with Active Directory recovery methods
- What are Windows 10 disk management terms IT should know?
- Working with PowerShell Secret Management and Secret Vault
- Microsoft 365 license plan vs. SKU vs. service plan vs. GUID vs. string ID
Related Terms
What is defragmentation? Defragmentation, also known as 'defragging' or 'defrag,' is the process of rearranging the data on a storage medium, such as a ... See complete definition What is NTFS and how does it work? NTFS, which stands for NT file system and the New Technology File System, is the file system that many versions of the Windows ... See complete definition What is the blue screen of death (BSOD)? The blue screen of death (BSOD) -- also known as a stop error screen, blue screen error, fatal error or bugcheck -- is a critical... See complete definitionDig Deeper on IT operations and infrastructure management
-
![]()
What is a UUID (Universally Unique Identifier)?
 By: Scott Robinson
By: Scott Robinson -
![]()
What is Pretty Good Privacy and how does it work?
 By: Alexander Gillis
By: Alexander Gillis -
![]()
What is a checksum?
 By: Rahul Awati
By: Rahul Awati -
![]()
hashing
 By: Kinza Yasar
By: Kinza Yasar
- 3 Strategies to Enhance Healthcare Financial Experiences –Zelis Healthcare
- Autonomous coding: The future of the revenue cycle –Solventum
- See More
- Computer Weekly – 7 October 2025: Is digital ID scheme doomed to fail? –TechTarget ComputerWeekly.com
- The future of API management: Key trends for IT leaders –TechTarget ComputerWeekly.com
- Cloud Computing
- Enterprise Desktop
- Virtual Desktop
- GenAI drives $119B cloud revenue in Q4
Q4 cloud infrastructure service revenues reach $119.1 billion, bringing the 2025 total to $419 billion. See how much market share...
- Cloud infrastructure suffers AI growing pains
Will $5 trillion in AI infrastructure investment be enough? Cloud providers facing that question must also yield a return, ...
- 8 reasons why IT leaders are embracing cloud repatriation
As IT leaders aggressively re-allocate capital to fund new AI initiatives, repatriation offers both savings and greater control, ...
- 6 reasons enterprise AI adoption starts small
Enterprise AI adoption starts small by design, shaped by integration limits, data readiness, governance discipline and ...
- How to build a plan for PC and desktop lifecycle management
Organizations can choose in-house, device-as-a-service or hybrid models for desktop lifecycle management, balancing cost, ...
- Will 2026 be the year deepfakes go mainstream?
Deepfakes are now so easy to create that anyone with a browser can make one. With cheap tools and abundant data, 2026 could be ...
- How to configure the Remote Desktop Users group in Windows
Managing the Remote Desktop Users group is essential for secure Windows access. IT teams should know how to configure it properly...
- How to enable and manage Windows 11 Hyper-V
Hyper-V virtual machines have many use cases in enterprise IT. Windows administrators should follow these steps to create new VMs...
- Understanding the DaaS options for Macs
When people discuss desktop as a service, it is usually in the context of Windows desktops. For macOS, however, implementing DaaS...
Tag » Active Directory Ldap Unique Identifier
-
A Unique ID Number For Active Directory Accounts That Could Be ...
-
Need To Get Unique User Identifier In Active Directory
-
How To Get Unique ID Of LDAP UserName - MSDN - Microsoft
-
UniqueIdentifier - Ldapwiki
-
What Active Directory Field Do I Use To Uniquely Identify A User?
-
Change Ldap Servers And User Unique ID Attribute
-
Authenticating Users With LDAP Registries In A Microsoft Active ... - IBM
-
Configuring Identity Federation - NetApp
-
Specifying The Global ID Attribute For Users And Groups
-
How Do You Change The Unique Identifier Used In An LDAP Import To ...
-
How To Find An Active Directory Object From The Globally Unique ...
-
Configuring Security Identifier (SID) For LDAP Users - Check Point
-
Specify The Global ID Attribute For Users And Groups
-
Integrate Active Directory Using Directory Utility On Mac



