What Is National Identity Card? - Definition From
Maybe your like
- Home
- Application and platform security
 By
By - Katie Terrell Hanna
What is a national identity card?
A national identity card is a portable document, typically a plasticized card with embedded personally identifiable information (PII) or data, that's used to verify a person's identity. It is issued by a government or state as proof of a person's identity and citizenship.
Which countries use national identity cards?
National identity cards are used in many countries, but their appearance, the data they contain and their functions can vary. Also, some countries require all citizens to have and carry a national identity card, while others issue them on a voluntary basis.
Some countries, like the United States, with robust passport systems or other forms of identity documents, do not issue national identity cards.
National identity cards can also serve various functions beyond identity verification, such as a travel document within certain regions, proof of eligibility to work, or access to government services and benefits.
What is included on a national identity card?
In general, a national identity card includes the following information:
- Full name.
- Photograph.
- Date of birth.
- Gender.
- Nationality.
- Card number.
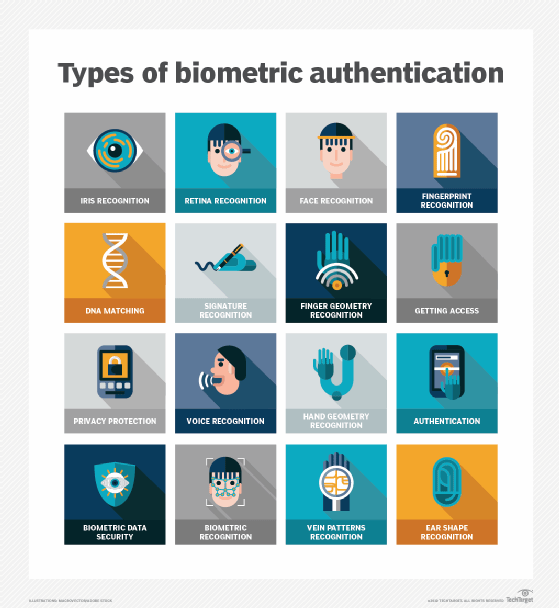
In some countries, additional information might also be included, such as the cardholder's address, marital status or even biometric data such as fingerprints.
Controversy behind national identity card
The concept of national identity card has always been a contentious issue, with arguments both for and against their implementation. The controversy often centers around the balance between enhancing security and protecting individual privacy rights.
The terrorist attacks on September 11, 2001, had a significant impact on the discourse around national identity cards, particularly in countries such as the United States, which do not have a national ID system. In the aftermath of the attacks, there were calls to implement such a system as a means of enhancing national security and preventing future acts of terrorism.
However, critics argue that national identity cards infringe on personal privacy and could potentially lead to a surveillance state. Furthermore, there is concern that mandatory identity cards would infringe on civil liberties and individual freedoms, potentially enabling discrimination or profiling.
There's also a fear of misuse of personal data, either by government entities or through data breaches. But misuse isn't the only challenge facing implementers of national identity cards.
The logistics of implementing a national identity card system can be challenging, particularly ensuring that all citizens are able to access their cards. The cost of implementing and maintaining such a system can also be substantial.
Finally, there is a question of whether national identity cards are effective at preventing crimes, fraud or terrorism. Some argue that resources would be better spent on other security measures.
In the U.S., the fallout from 9/11 led to changes in identity verification with the REAL ID Act of 2005 setting new standards for state-issued driver's licenses and identification cards. These policies are enforced by the federal government for official purposes such as boarding commercially operated airline flights.
Learn the difference between identity management vs. authentication.
Continue Reading About national identity card
- Use a decentralized identity framework to reduce enterprise risk
- Paid verification explained: Everything you need to know
- Centralized vs. decentralized identity management explained
- In biometrics, security concerns span technical, legal and ethical
- 4 identity predictions for this year
Related Terms
What is a message authentication code (MAC)? How it works and best practices A message authentication code (MAC) is a cryptographic checksum applied to a message to guarantee its integrity and authenticity. See complete definition What is file integrity monitoring (FIM)? File Integrity Monitoring (FIM) is a security process that continuously monitors and analyzes the integrity of an organization's ... See complete definition What is governance, risk and compliance (GRC)? Governance, risk and compliance (GRC) refers to an organization's strategy, or framework, for handling the interdependencies of ... See complete definitionDig Deeper on Application and platform security
-
![]()
Government considers physical ID cards
 By: Lis Evenstad
By: Lis Evenstad -
![]()
What is a SIM card and how does it work?
 By: Scott Robinson
By: Scott Robinson -
![]()
What is Secure Digital Extended Capacity card (SDXC)?
 By: Rahul Awati
By: Rahul Awati -
![]()
What is a CompactFlash card (CF card)?
 By: Paul Kirvan
By: Paul Kirvan
- A spotlight on food is medicine: Creating sustainable programs –Zelis Healthcare
- Key elements of effective member incentive programs –Zelis Healthcare
- See More
- CW ASEAN November 2016 –TechTarget Security
- Why HSMs Are the Key to Quantum-Safe Security –Entrust, Inc.
- Networking
- CIO
- Enterprise Desktop
- Cloud Computing
- Computer Weekly
- 5 principles of change management in networking
Network change management includes five principles, including risk analysis and peer review. These best practices can help ...
- How network efficiency advances ESG goals
From SDN to green electricity, network optimization plays a critical role in helping enterprises reduce emissions, cut costs and ...
- How to build a private 5G network architecture
A private 5G network can provide organizations with a powerful new option for their wireless environments. Here are the major ...
- How big tech AI talent poaching affects the AI talent wars
Big tech companies are fiercely competing for AI talent. These talent wars drive up compensation, use aggressive strategies to ...
- What CIOs can learn from Marc Benioff's ICE joke
Marc Benioff's ICE agent joke at a Salesforce all-hands meeting puts spotlight on IT system and operational risks with ...
- AI workforce training: How BDO USA trains its employees
Getting employees comfortable with AI is tough for CIOs. BDO USA uses AI ambassadors, tailored training and a virtual escape room...
- How end-user computing is becoming a cost-control system
End-user computing has shifted from desktop support to a financial control plane, exposing SaaS sprawl, labor inefficiency and ...
- The promise and concern around end-user AI second brains
Human-delegated AI agents and "second brains" could transform knowledge work, but only if IT can balance governance, data ...
- How Windows 11 Safe Mode works and when to use it
Windows 11 Safe Mode gives IT leaders a reliable way to diagnose failures, restore access to broken systems and strengthen ...
- 3 FinOps trends to look out for in 2026
FinOps is evolving beyond its traditional focus on cost reduction into a strategic framework for driving business value. Discover...
- Top enterprise hybrid cloud management tools to review
The techniques used to build hybrid cloud architectures have come a long way, but managing these environments long term is plenty...
- GenAI drives $119B cloud revenue in Q4
Q4 cloud infrastructure service revenues reach $119.1 billion, bringing the 2025 total to $419 billion. See how much market share...
- Electronic health records are still creating issues for patients
Almost every NHS trust will have moved onto a digital system by this spring. Experts have cautioned many patients are still ...
- Sweden recommends citizens keep £81 in cash per adult in case of payment system crash
The central bank of Sweden says rapid digitisation could cause vulnerabilities in payment systems
- Spyware suppliers exploit more zero-days than nation states
Exploitation of zero-days by commercial surveillance and spyware developers outpaced exploitation by nation-state actors last ...
Tag » What Is A National Identity Card
-
List Of National Identity Card Policies By Country - Wikipedia
-
National Identification Number - Wikipedia
-
What Is A National ID Card? (National ID, Digital ID) - Thales
-
A National Identity Card For Hong Kong - Thales
-
Identity Card, Passport And Other Documents - ICA
-
National Identity Cards - IDEMIA
-
National Identity Card - Bmi.
-
National Identity Card - Immigration And Citizenship
-
National ID Card - UDI
-
5 Problems With National ID Cards | American Civil Liberties Union
-
National Digital Identity - Smart Nation Singapore
-
About The E-ID Card - National Identity Management Commission
-
National Identification Cards | The First Amendment Encyclopedia



