Vulnerability Assessment (vulnerability Analysis) By - TechTarget
Có thể bạn quan tâm
- Home
- Risk management
- TechTarget Contributor
What is a vulnerability assessment?
A vulnerability assessment is the process of defining, identifying, classifying and prioritizing vulnerabilities in computer systems, applications and network infrastructures.
Vulnerability assessments provide organizations with the necessary knowledge, awareness and risk backgrounds to understand and react to threats to their environment.
A vulnerability assessment intends to identify threats and the risks they pose. It typically involves using automated testing tools, such as network security scanners, whose results are listed in a vulnerability assessment report.
Organizations of any size, or even individuals who face an increased risk of cyberattacks, can benefit from some form of vulnerability assessment, but large enterprises and organizations subject to ongoing attacks will benefit most from vulnerability analysis.
Because security vulnerabilities enable hackers to access IT systems and applications, it is essential for enterprises to identify and remediate weaknesses before they can be exploited. A comprehensive vulnerability assessment, along with a vulnerability management program, can help companies improve the security of their systems.
Importance of vulnerability assessments
Vulnerability assessments provide organizations with details on security weaknesses in their environments. They also provide directions on how to assess the risks associated with those weaknesses. This process offers the organization a better understanding of assets, security flaws and overall risk, reducing the likelihood a cybercriminal will breach their systems.
Types of vulnerability assessments
Vulnerability assessments discover different types of system or network vulnerabilities. The assessment process includes using a variety of tools, scanners and methodologies to identify vulnerabilities, threats and risks.
Types of vulnerability assessment scans include the following:
- Network-based scans identify possible network security attacks. This type of scan can also detect vulnerable systems on wired or wireless networks.
- Host-based scans locate and identify vulnerabilities in servers, workstations or other network hosts. This scan usually examines ports and services that could be visible on network-based scans. It offers greater visibility into the configuration settings and patch history of scanned systems, even legacy systems.
- Wireless network scans focus on points of attack in wireless network infrastructure. In addition to identifying rogue access points, a wireless network scan also validates a company's network is securely configured.
- Application scans test websites to detect known software vulnerabilities and incorrect configurations in network or web applications.
- Database scans identify weak points in a database to prevent malicious attacks, such as SQL injection attacks.
Vulnerability assessments vs. penetration tests
A vulnerability assessment often includes a pen testing component to identify vulnerabilities in an organization's personnel, procedures or processes. These vulnerabilities might not normally be detectable with network or system scans. The process is sometimes referred to as vulnerability assessment/penetration testing, or VAPT.
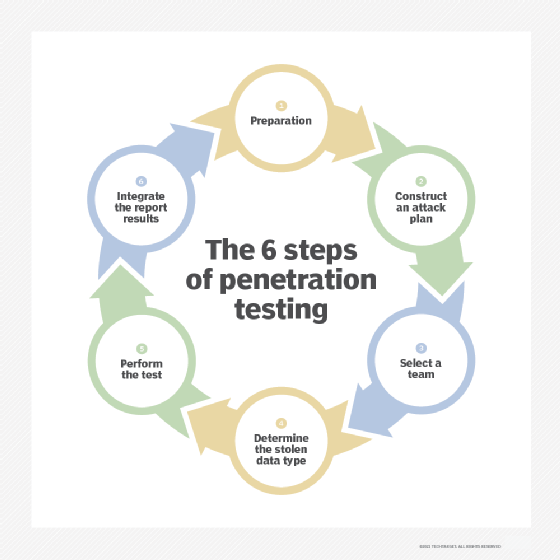
Pen testing is not sufficient as a complete vulnerability assessment and is, in fact, a separate process. A vulnerability assessment aims to uncover vulnerabilities in a network and recommend the appropriate mitigation or remediation to reduce or remove the risks.
A vulnerability assessment uses automated network security scanning tools. The results are listed in a vulnerability assessment report, which focuses on providing enterprises with a list of vulnerabilities that need to be fixed. However, it does so without evaluating specific attack goals or scenarios.
Organizations should conduct vulnerability testing on a regular basis to ensure the security of their networks, particularly when changes are made. For example, test when services are added, new equipment is installed or ports are opened.
In contrast, pen testing involves identifying vulnerabilities in a network and then attempting to exploit those vulnerabilities to attack the system. Although sometimes carried out in concert with vulnerability assessments, the primary aim of pen testing is to check whether a vulnerability exists. In addition, pen testing tries to prove that exploiting a vulnerability can damage the application or network.
While a vulnerability assessment is usually automated to cover a wide variety of unpatched vulnerabilities, pen testing generally combines automated and manual techniques to help testers delve further into the vulnerabilities and exploit them to gain access to the network in a controlled environment.
This article was written by a TechTarget Contributor in 2021. TechTarget editors revised it in 2024 to improve the reader experience.
Continue Reading About vulnerability assessment
- Compare vulnerability assessment vs. vulnerability management
- Types of vulnerability scanning and when to use each
- Risk and vulnerability assessments - CISA
- How to conduct a cyber-resilience assessment
- What is attack surface management and why is it necessary?
Related Terms
What is governance, risk and compliance (GRC)? Governance, risk and compliance (GRC) refers to an organization's strategy, or framework, for handling the interdependencies of ... See complete definition What is integrated risk management (IRM)? Integrated risk management (IRM) is a set of proactive, businesswide practices that contribute to an organization's security, ... See complete definition What is the three lines model and what is its purpose? The three lines model is a risk management approach to help organizations identify and manage risks effectively by creating three... See complete definitionDig Deeper on Risk management
-
![]()
What is penetration testing?
 By: Kinza Yasar
By: Kinza Yasar -
![]()
Top 14 open source penetration testing tools
 By: Ed Moyle
By: Ed Moyle -
![]()
Penetration testing vs. vulnerability scanning: What's the difference?
 By: Kyle Johnson
By: Kyle Johnson -
![]()
What is network scanning? How to, types and best practices
 By: Paul Kirvan
By: Paul Kirvan
- Best Practices: Preparing for the Inevitable Healthcare Cyberattack –Commvault + Microsoft
- The ROI of Interoperability in Value-Based Models –Veradigm
- See More
- Speed Up The Routeto Pci Dss Compliance –Pcysys
- 11 Open Source Automated Penetration Testing Tools –TechTarget
- Networking
- CIO
- Enterprise Desktop
- Cloud Computing
- Computer Weekly
- How network modernization creates measurable ROI
Modern networks improve performance, resiliency, security and flexibility. These gains translate into measurable direct and ...
- 5 principles of change management in networking
Network change management includes five principles, including risk analysis and peer review. These best practices can help ...
- How network efficiency advances ESG goals
From SDN to green electricity, network optimization plays a critical role in helping enterprises reduce emissions, cut costs and ...
- Surveillance backlash: A wake-up call for CIOs
Ring's abandoned Flock Safety partnership shows how AI surveillance and third-party integrations can spark backlash, highlighting...
- How to upskill in AI: Lessons from a CIO
Sedgwick CIO Sean Safieh explains how CIOs can use course-based training, hands-on learning and safe experimentation to lead AI ...
- The psychology behind AI resistance: What CIOs need to know
AI is reshaping the way the world does business at breakneck speed, yet many CIOs are facing adoption resistance because of how ...
- How IT can use the gpresult command to check GPOs
Desktop admins can use the gpresult command to identify which Group Policy Objects apply to a system and troubleshoot ...
- Setting up Windows 11 kiosk mode with 4 different methods
Windows 11 kiosk mode allows IT to restrict devices to specific apps. There are four deployment methods: local setup, PowerShell,...
- How to find the best laptops for enterprise software workloads
Laptop procurement decisions increasingly begin with software requirements. Discover how workloads, security tools and ...
- Multi-cloud vs. hybrid cloud: The main difference
As businesses digitally transform across increasingly distributed environments, know the benefits, challenges, similarities and ...
- How autonomous AI workloads reshape cloud cost management
AI workloads break traditional cloud cost models. As agents and inference loops drive spend, organizations must embed ...
- Top AWS tools for cloud cost forecasting
Unpredictable AWS spending creates financial planning challenges for executives, but native tools can transform reactive cost ...
- Interpol obliterates cyber criminal infrastructure
A major Interpol operation has resulted in the seizure of thousands of malicious cyber criminal IP addresses and servers, and ...
- How CISOs can build a truly unified and resilient security platform
The Security Think Tank looks at platformisation, considering questions such as how CISOs can distinguish between a truly ...
- Shared Rural Network expansion removes Islay not-spots
Latest development in £1.3bn mobile expansion scheme sees mobile not-spots reduced on Scottish island as 4G site goes live, ...
Từ khóa » Vulnerability Safety Risk Assessment
-
How To Use A Risk Assessment Vs. A Vulnerability ... - SoftwareONE
-
[PDF] Vulnerability And Risk Assessment
-
Risk Assessment Vs Vulnerability Assessment: How To Use Both
-
How To Define Risks During A Vulnerability Assessment? - Indusface
-
Risk Assessment Vs Vulnerability Assessment - HackerNoon
-
Risk Assessment Vs Vulnerability Assessment: How Companies ...
-
[PDF] ANALYZE CAPABILITIES, RISKS, & VULNERABILITIES - OSHA
-
[PDF] A Safety Vulnerability Assessment For Chemical Enterprises
-
Using Risk And Vulnerability Assessments To Increase Physical ...
-
VULNERABILITY SCANS AND RISK ASSESSMENTS
-
Risk & Vulnerability Assessments
-
Threat / Vulnerability Assessments And Risk Analysis | WBDG
-
Develop Preliminary Vulnerability And Risk Assessment (e)



