What Is A Hardware Security Module? - TechTarget
Có thể bạn quan tâm
- Home
- Data security and privacy
- Rahul Awati
- Elizabeth Davies
- Cameron McKenzie, TechTarget
A hardware security module (HSM) is a physical device that provides extra security for sensitive data. HSMs are security-hardened, intrusion-resistant and tamper-resistant pieces of hardware that are used to provision cryptographic keys for critical functions such as encryption, decryption and authentication for the use of applications, identities and databases. Simply put, they function as trust anchors for cryptographic operations. The most reliable HSMs are aligned (validated and certified) with the strongest globally accepted security standards like Federal Information Processing Standardization (FIPS) 140-2 and FIPS 140-3.
What does a hardware security module do?
The hardware security module protects cryptographic keys and handles the encryption and decryption processes. By securely generating, protecting and managing these public and private keys, HSMs help to secure cryptographic processes and the transactions and data they are meant to protect.
Businesses use HSMs to keep these cryptographic functions, particularly related to transactions, identities and applications, separate from regular operations and to control access to those functions. For example, a company might use an HSM to secure trade secrets or intellectual property by ensuring only authorized individuals can access the HSM to complete a cryptography key transfer. In doing so, organizations can better protect their sensitive data from unauthorized or malicious parties, and ensure the integrity of transactions.
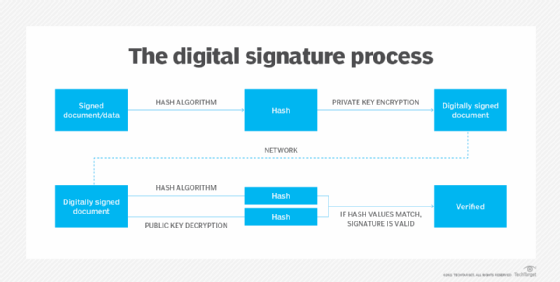
HSMs can also create and verify digital signatures. By helping with the secure generation and storage of cryptographic keys, HSMs make it possible for users and certificate authorities to create and verify digital signatures. These signatures then help to authenticate users and validate their digital transactions, thus ensuring data integrity and preventing impersonation and tampering. In addition to digital signing and key generation and management, these devices are also used for ensuring compliance, simplifying transaction audits and for securing data and digital identities.
As the global cyberthreat landscape expands, HSMs have emerged as a crucial element of data security for enterprises around the world. They provide the centralized key generation, management and storage, as well as authentication and digital signing capabilities that modern businesses need to operate in today's digital economy. Embracing HSM technology also provides companies with the flexibility needed to keep up with the move to the cloud.
Hardware security modules and data protection
Any business that handles valuable or sensitive information, such as credit or debit card data, intellectual property, customer data and employee information, should consider using a hardware security module. By providing a hardened, isolated environment, HSMs can safeguard this data from tampering, compromise and theft.
HSMs secure the data generated by a range of applications:
- Websites.
- Banking apps.
- Mobile payments.
- Cryptocurrencies.
- Smart meters.
- Medical devices.
- Identity cards and personal identification numbers (PINs).
- Digital documents.
HSMs can also secure the data involved in financial transactions. The Payment Card Industry Data Security Standard (PCI DSS) recommends using specialized HSMs that provide the added security features required for such transactions. These devices support applications like PIN management, provision of payment card and mobile app credentials, and verification capabilities for PINs, payment cards and other functions.
How do hardware security modules work?
Securing the keys in a cryptographic system is critical to maintaining a secure system. However, managing the lifecycle of those keys is a challenge. HSMs can ease the burden of that challenge by performing all the cryptographic functions required to secure data during digital transmissions, thus providing protection for sensitive private keys while also simplifying user experiences for authorized users.
An HSM accepts an authorized user's request for a cryptographic operation. The request, for instance "sign a digital certificate," acts as the HSM's input. On receiving the input, the HSM signs the digital certificate using the private key that is stored within its confines. It then generates the signed digital certificate, allowing the transaction to proceed. The users or applications involved in the transaction cannot see or access -- much less alter -- the cryptographic keys since all the input/output functions are executed inside the HSM's secure and isolated environment.
Benefits of hardware security modules
HSMs improve both data and IT systems security, making them ideal for any organization looking to protect its cryptographic keys from exposure and compromise. The private key required to decrypt a piece of encrypted information does not leave the HSM, and cannot end up on another entity such as an internet-connected web server's memory, where it could be vulnerable to all kinds of cyberattacks.
By performing all cryptographic functions within its secure confines, the HSM protects the private key from being accessed or compromised by hackers, safeguards sensitive data and ensures that the transaction is limited to authorized parties only. At the same time, the keys can be used by authorized users -- even while they don't have direct access to them. In this way, the HSM ensures that user experiences are not affected. Furthermore, the devices enable businesses to move sensitive information and processes from paper documentation to a digital format.
Organizations can use HSMs to secure the keys for any environment: development, testing or production. This allows users (as well as software and systems) to confidently use their internal environments without needing to directly access the keys.
HSMs keep the keys secure throughout every lifecycle stage, from generation and storage, to archival and revocation/disposal. In this way, they reduce the attack surface and ensure that the keys (and the data they are meant to safeguard) remain protected, even when not in use.
Another benefit of HSMs is that they perform cryptographic operations without needing to involve servers. This is because HSMs are designed as standalone devices with operational capabilities. By taking on cryptographic operations, HSMs can help to accelerate web traffic. Also, multiple HSMs can be used together to deliver public key management and minimize impact on an application's speed.
Next, all access transactions involving an HSM are logged to create an audit trail. The logs provide useful information about what cryptographic operations were performed by the HSM, when they were performed and who authorized them. Organizations can use these logs to maintain the integrity and accountability of transactions and users.
Finally, HSMs are manufactured to meet widely accepted security standards like FIPS 140-2 and Common Criteria for Information Technology Security Evaluation (Common Criteria). Alignment with these standards allows the organizations that use HSMs for cryptographic purposes to maintain compliance with various regulations for data security and privacy.
Cryptography lifecycle managed by HSMs
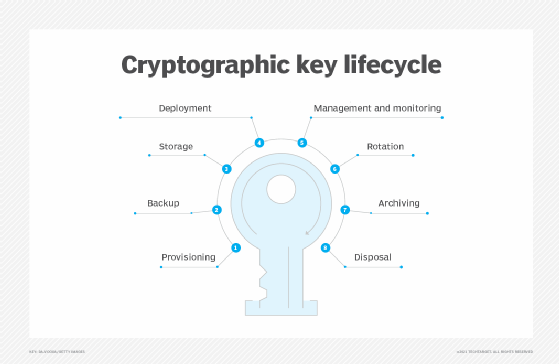
Regardless of type, HSMs securely manage all the aspects of a cryptography key's lifecycle, including the following:
- Key provisioning. Key provisioning is when HSMs create a unique key that will be used to encrypt the transaction data before it is transmitted over a digital network. Most HSMs include random number generators that generate truly random keys that are harder to compromise.
- Backup and storage. HSMs ensure that a copy of the keys is made and securely stored to enable retrieval in case of compromise or loss. The keys can be stored and backed up in the HSM or on external media. Private keys must be encrypted before being stored.
- Deployment. This step involves installing the key in the HSM.
- Management. The HSM controls and monitors the keys based on industry standards and an organization's own internal policies. Also, its encryption key management system handles key rotation where new keys are deployed as existing keys expire.
- Archiving. The HSM will store decommissioned keys in offline, long-term storage for when they may be needed to access existing data that was encrypted with the archived keys.
- Disposal. If it is determined that the keys are no longer needed, the HSM will securely and permanently destroy them, ensuring that they cannot be reused or compromised.
Important HSM features
The following features of HSMs contribute to their security capabilities:
- Secure design. HSMs use specially designed hardware that adheres to widely accepted security standards such as FIPS 140-2, Common Criteria and the PCI's HSM requirements.
- Tamper resistant. HSMs undergo a hardening process to make them resistant to illicit tampering and unintentional damage.
- Secure operating system. HSMs have a security-focused operating system.
- Isolated. HSMs are located in a secure physical area of a data center to prevent unauthorized access. Some organizations opt to store their HSMs in a third-party data center, rather than keeping them on site.
- Access controls. HSMs control access to the devices and the data they protect. They are designed to show signs of tampering; some HSMs become inoperable or delete cryptographic keys if tampering is detected.
- APIs. HSMs support a range of application programming interfaces that enable application integration and the development of custom applications, including the Public-Key Cryptography Standard and Cryptography API Next Generation.
Types of hardware security modules
HSMs can be plugin cards or embedded in other hardware, including smart cards, appliances and other external devices. They can be connected to a network server or used as a standalone device offline.
Increasingly, HSMs are also offered as cloud services, often referred to as HSM as a service, a subscription-based offering that organizations can use over the internet to securely generate, access and protect cryptographic keys. Organizations can also deploy both as-a-service HSMs and on-premises HSMs, depending on their cryptographic requirements, technology budget and cloud-first objectives.
HSMs, cloud computing and cloud-based key management as a service
The advent of cloud computing has complicated the process of securing sensitive data, as more of it has moved to the cloud. On-premises HSM devices cannot always be used in cloud environments so cloud service providers (CSPs) require customers to use HSMs hosted in the CSP's data centers. Even if a CSP allows the use of on-prem HSMs, connectivity issues can introduce unwanted latency into the system.
Another challenge related to cloud computing is how to manage keys. While most large cloud vendors provide their own key management services, those services are not always usable across hybrid cloud and multi-cloud environments. Consequently, customers have to deal with the complexities of multiple key management tools to accommodate their hybrid and multi-cloud needs.
Key management as a service provides a way to easily secure and manage encryption keys across different cloud environments. KMaaS services offer centralized, on-demand HSM-level tools without the need for organizations to provision their own complex, expensive hardware. Thus, as a business expands and uses more cloud services (particularly in hybrid or multi-cloud environments), it can use the same KMaaS offering to deploy and manage all the encryption keys needed across multiple clouds and CSPs.
To ensure the same level of security as on-premises HSMs, KMaaS products adhere to the same standards as the locally installed devices. They also support a variety of APIs to facilitate seamless interactions with outside services. With these systems, encryption key management functions take place at a digital edge node, minimizing latency and improving application performance without compromising security.
AWS, Google, IBM and Microsoft all offer cloud KMaaS products, along with smaller companies such as Entrust and Thales.
Data security and privacy compliance
Hardware security modules are at the center of data security and privacy issues. Because of the key role they play, they are under increased scrutiny, as business and other organizations face increasing security threats. More specialized HSMs must comply with a range of standards and regulations, including the following:
- European Union's General Data Protection Regulation.
- PCI DSS.
- Domain Name System Security Extensions.
- FIPS 140-2.
- Common Criteria.
Learn more about all aspects of data protection and compliance in our comprehensive guide to data security.
Continue Reading About What is a hardware security module?
- Optimize encryption and key management
- How to use a public key and private key in digital signatures
- Symmetric key encryption algorithms and security: A guide
- Cloud security: Finding the right provider to protect your data
- Cryptography quiz questions and answers: Test your smarts
Related Terms
What is a backup storage device? A backup storage device is a hardware component that stores duplicate copies of data. See complete definition What is antivirus software? Antivirus software (antivirus program) is a security program designed to prevent, detect, search and remove viruses and other ... See complete definition What is data masking? Data masking is a security technique that modifies sensitive data in a data set so it can be used safely in a non-production ... See complete definitionDig Deeper on Data security and privacy
-
![]()
What is hardware security?
 By: Nick Barney
By: Nick Barney -
![]()
The cloud's role in PQC migration
 By: George Lawton
By: George Lawton -
![]()
How to choose a cloud key management service
 By: Dave Shackleford
By: Dave Shackleford -
![]()
What is machine identity management?
 By: Sean Kerner
By: Sean Kerner
- 3 Strategies to Enhance Healthcare Financial Experiences –Zelis Healthcare
- The growing role of the healthcare CFO –Huron
- See More
- Strengthening Credential Management with Secure Key Handling –Utimaco
- Code and document signing with Keyfactor SignServer and Utimaco HSMs –Utimaco
- Networking
- CIO
- Enterprise Desktop
- Cloud Computing
- Computer Weekly
- Macrocell vs. small cell vs. femtocell: A 5G introduction
Macrocells, small cells and femtocells each play distinct roles in 5G, balancing coverage, speed, cost and indoor connectivity ...
- What are the features and benefits of 5G technology?
Increased cellular speed, bandwidth and capacity at lower latencies have made wireless VR and AR practical for business use, ...
- Wi-Fi 6 vs. 5G: What's the difference?
Wi-Fi 6 and 5G both boost speed and performance, but differ in cost, coverage and use cases. Together, they provide flexible ...
- From CIO to CEO: Unlocking the entire C-suite
CIOs can evolve from technology leaders to enterprise strategists, taking on higher C-suite roles by building profit and loss ...
- How AI Is reshaping IT leadership and the modern CIO
Internal IT succession planning develops CIO-ready leaders, reduces disruption and strengthens organizational resilience through ...
- Predictable IT spending in an unpredictable economy
As AI and volatility push costs higher, CIOs must adopt flexible budgeting -- rolling forecasts, FinOps and real-time metrics -- ...
- How to use Windows Check Disk to maintain disk health
Using built-in Windows tools such as Check Disk and SMART helps organizations reduce risks associated with disk errors, extend ...
- How IT admins can check BIOS or UEFI versions in Windows 11
Firmware, such as BIOS or UEFI, plays a crucial role in how securely a Windows device starts and operates. Organizations need to ...
- Microsoft opens Copilot agent building to office rank and file
The battle for desktop agent mindshare heats up. Microsoft is the latest to arm everyday office workers with tools to make their ...
- Nutanix sovereign cloud hits Broadcom with multi-cloud hook
Nutanix expands its differentiation from Broadcom with a distributed sovereign cloud approach that supports both self-managed and...
- Plan for repatriation on day one with a hybrid cloud strategy
In the next 2 years, 87% of orgs plan to repatriate workloads off public cloud. Discover how an exit strategy, paired with hybrid...
- AWS CloudOps hones multi-cloud support for AI, resilience
Network, observability and Kubernetes management news at re:Invent aligned around themes of multi-cloud scale and resilience amid...
- Top 10 India stories of 2025
From infrastructure expansion and sovereign AI innovation to regulatory maturity, Computer Weekly recaps the key developments ...
- Top 10 networking stories of 2025
As enterprises become more extended, dealing with network complexity has become almost as important as network performance. The ...
- Top 10 cyber crime stories of 2025
In many regards, 2025 proved to be a relatively normal year for the cyber security world as threat actors and security pros ...
Từ khóa » Hsm Flow
-
HSM Flow With Both Authentication And Encryption - 2022.1 English
-
What Is A Payment Hardware Security Module (HSM)? - Thales
-
Security HSM - AWS CloudHSM - Amazon Web Services
-
Understanding Hardware Security Modules (HSMs) - Cryptomathic
-
Hardware Security Module (HSM) | SWIFT - The Global Provider Of ...
-
How Does Hardware Security Module (HSM) Protect Payment Card ...
-
HSM Operation Flow Chart | Download Scientific Diagram
-
The Role Of HSM In Credit Card Payment And Retail Banking
-
Data Encryption Hardware Security Module Hsm - Atos
-
Interaction Between The HSM And The PED
-
Network Hardware Security Module (HSM) - Kemp Support
-
Hydro Structural Modelling - HSM - Seequent



